The RADIUS server is one of the most critical components in the infrastructure of any internet service provider. It ensures client authentication when connecting via PPPoE, IPoE, or hotspot, and often also authenticates technicians when they access the network. As long as it operates properly, everything runs smoothly. However, if the primary RADIUS server fails, a major issue can affect the entire network within minutes.
That is why ISPadmin offers a solution in the form of the Backup RADIUS Server submodule, designed to minimize the risk of authentication outages and help keep services fully operational even in the event of technical complications.
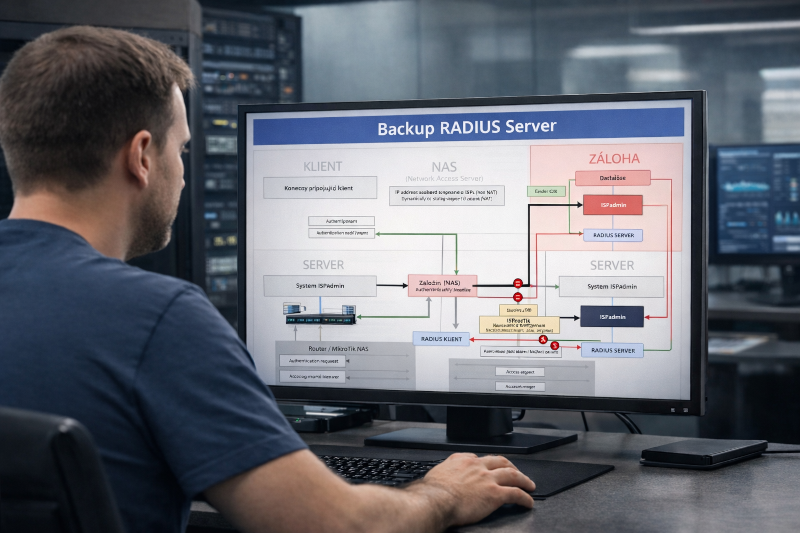
How the Backup RADIUS Works?
The Backup RADIUS Server submodule extends the RADIUS module and allows you to run a separate ISPadmin installation as a secondary authentication server. This installation operates on a separate server or virtual machine and serves as a full replacement for the primary RADIUS server in case it becomes unavailable.
Authentication data is synchronized between the primary and backup servers, ensuring that the secondary instance always contains up-to-date information required to verify both clients and technicians. If the primary server goes down, network devices automatically switch to the secondary RADIUS server, allowing authentication to continue without interruption.
An important part of the solution is update automation. When the primary ISPadmin installation is updated, the backup instance is also updated via SSH, eliminating the need to manage two servers separately.
Ready for MikroTik and Other Devices
ISPadmin can automatically write both primary and backup RADIUS server parameters to registered MikroTik devices. This ensures routers are prepared for a failover scenario without requiring manual configuration on each device. If the primary RADIUS server does not respond, devices seamlessly switch to the secondary server.
This approach significantly reduces the risk of widespread outages during maintenance, hardware failures, or virtualization platform issues.
Why One Server Is Not Enough?
Many ISPs operate RADIUS on a single server instance, often within the same infrastructure as other critical services. Such a setup represents a single point of failure that can impact hundreds or even thousands of customers. A backup RADIUS located on the same hypervisor or in the same physical location does not fully eliminate the actual risk.
A properly designed architecture should include a separate server, ideally in a different location or at least on a different virtualization layer. Only this approach provides true redundancy.
Testing as Part of Operations
Deploying a backup RADIUS server should not be a mere formality. We recommend regularly verifying data synchronization and simulating a primary server outage to ensure that network devices genuinely switch to the secondary instance. Redundancy that is not tested does not provide real protection.
Who Is This Solution For?
The Backup RADIUS Server is particularly suitable for providers with higher stability and SLA requirements, ISPs with a larger customer base, or those who want to minimize the risk of outages during planned maintenance. Today, authentication stability is not just a technical matter — it is also an essential part of the overall customer experience.